H12-711_V4.0 Huawei HCIA-Security V4.0 Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Huawei H12-711_V4.0 HCIA-Security V4.0 Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which of the following protocols is a file transfer protocol?
Certificates saved in DER format may or may not contain a private key.
The RADIUS protocol specifies how to pass user information, billing information, authentication and billing results between the NAS and the RADIUS server, and the RADIUS server is responsible for receiving the user's connection request, completing the authentication, and returning the result to the NAS.
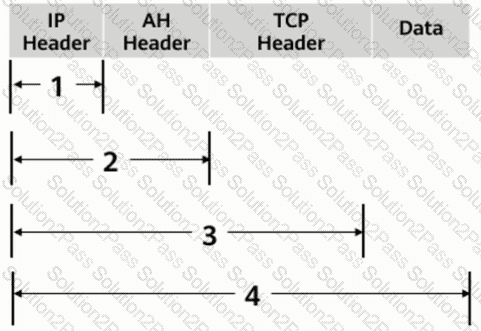
As shown in the figure, what is the range of the AH protocol authentication range in transmission mode?
Which of the following descriptions about the main implementation of single sign-on is wrong?
Which of the following characteristics does a denial-of-service attack include?
Which of the following types of malicious code on your computer includes?
SSL VPN is a VPN technology that realizes remote secure access through SSL protocol. Which of the following software must be installed when using SSL VPN?
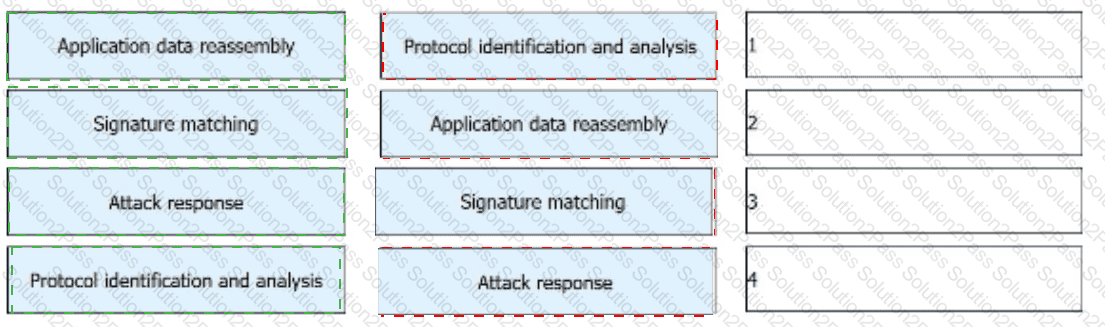
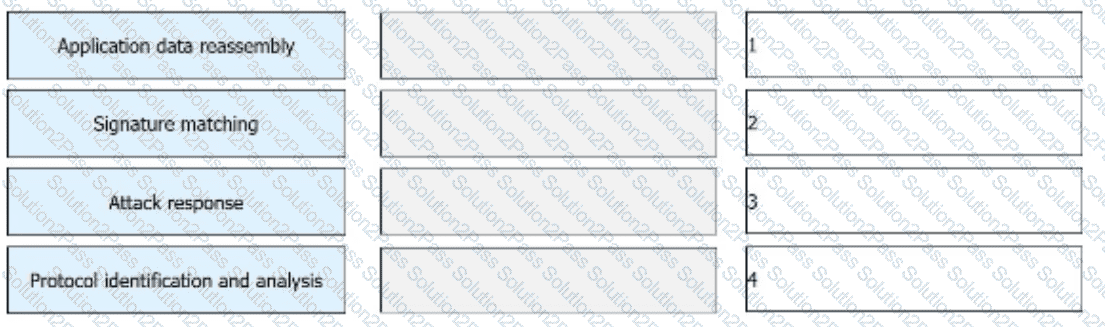
The IPS detects and analyzes all packets passing through a device and determines whether to permit or block the packets in real time based on the comprehensive detection mechanism. Sort the following steps into the correct order based on the basic implementation mechanism of the IPS.
Which of the following statements is correct about SSO?
As shown in the figure, the administrator needs to test the network quality of the 20.0.0/24 CIDR block to the 40.0.0/24 CIDR block on Device B, and the device needs to send large packets for a long time to test the network connectivity and stability.

Which of the following NAT technologies can implement a public network address to provide source address translation for multiple private network addresses ( )*
A Web server is deployed in an enterprise intranet to provide Web access services to Internet users, and in order to protect the access security of the server, it should be divided into the _____ area of the firewall.
Please match the following information security risks to information security incidents one by one.[fill in the blank]*
physical security risk Enterprise server permissions are loosely set
Information Security Management Risk Infected Panda Burning Incense
Information Access Risk Fire destroyed equipment in computer room
application risk Talk to people about leaking company secrets
Which of the following is not a type of Windows log event?
We should choose the encryption algorithm according to our own use characteristics. When we need to encrypt a large amount of data, it is recommended to use the ____ encryption algorithm to improve the encryption and decryption speed.[fill in the blank]*
Which of the following statements are correct about the PKI system structure?
In the authentication policy of the firewall, _____ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
Which of the following are application-layer protocols?
A three-way handshake is required to establish a TCP connection, and a four-way handshake is required to end a TCP connection.