H12-711_V4.0 Huawei HCIA-Security V4.0 Exam Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Huawei H12-711_V4.0 HCIA-Security V4.0 Exam certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
In most cases, a user applies for a local certificate from a CA, and the CA approves the application and issues the certificate to the user.
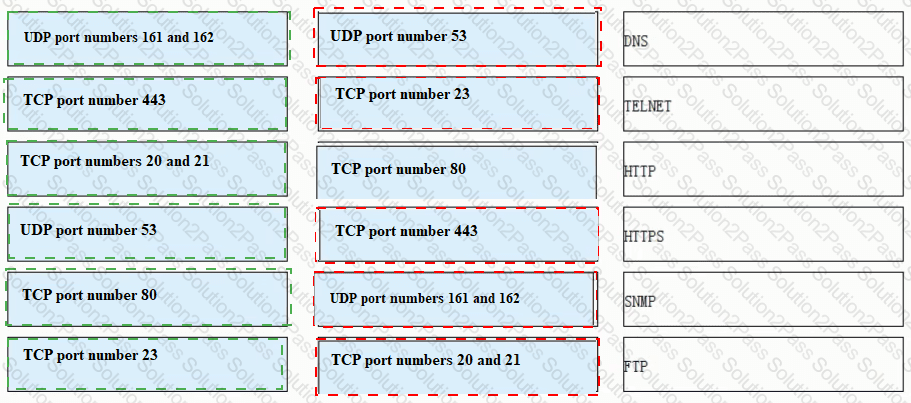
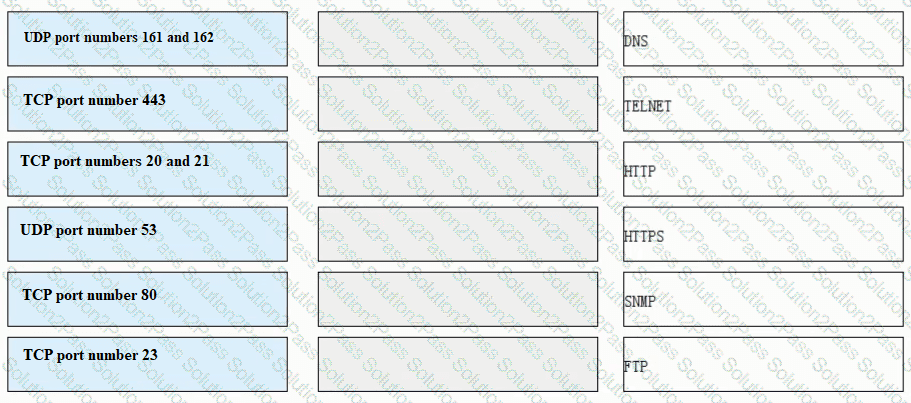
Match each of the following application layer service protocols with the correct transport layer protocols and port numbers.
Compared with the software architecture of C/S, B/S does not need to install a browser, and users are more flexible and convenient to use.
The following description of the AH protocol in IPSec VPN, which one is wrong?
An enterprise wants to build a server system and requires the following functions: 1. The enterprise needs to have its own dedicated mailbox, and the sending and receiving of emails needs to go through the enterprise's server; 2. The server must provide file transfer and access services. Users in different departments of the enterprise provide accounts with different permissions: 3. When the enterprise accesses the internal webpage of the enterprise, the enterprise can directly enter the domain name in the browser to access. To meet the above requirements, which of the following servers do enterprises need to deploy? ( )*
Which of the following statements are correct about the status of the firewall VGMP group?
The following description of digital certificates, which one is wrong
Which of the following functions help implement IPsec secure transmission of user service data on the Internet by means of encryption and authentication?
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.
Digital envelope technology means that the sender uses the receiver's public key to encrypt the data, and then sends the ciphertext to the receiver
In the TCP/P protocol core, which of the following protocols works at the application layer?
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?
Which of the following statements is correct about characteristics of a firewall?
Which of the following operating modes does NTP support?
What is correct about the following description of device management in the operating system?
HTTPS introduces the TLS layer based on HTTP to provide identity authentication, encryption, and integrity check for data transmission.
Which of the following problems cannot be solved using PKI?
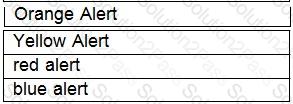
Drag the warning level of the network security emergency response on the left into the box on the right, and arrange it from top to bottom in order of severity.[fill in the blank]*
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol?