H12-891_V1.0 Huawei HCIE-Datacom V1.0 Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Huawei H12-891_V1.0 HCIE-Datacom V1.0 certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
Which of the following statements is incorrect about MP-BGP?
A network administrator runs the display telemetry destination command on a device to check information about a destination group that sampled data is sent to. The command output is as follows. Which of the following statements is incorrect?
[~CE-telemetry-sensor-group-Sensor1]display telemetry destination
Dest-name Dest-addr Dest-port State Vpn-name Protocol
Dest1 192.168.56.1 20000 RESOLVED - GRPC
During the implementation of iMaster NCE-Campus Wi-Fi location-based services (LBS), terminal location data is sent to an LBS platform through HTTP requests. Which of the following data formats is used in such HTTP requests?
Which of the following factors does not need to be considered during the selection of core devices for the enterprise bearer WAN?
In the firewall hot standby scenario, when VGMP works in load balancing mode, which of the following functions must be enabled on the firewalls to prevent the return traffic from being discarded because it does not match any session entry in the case of inconsistent forward and return paths?
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following fields is not carried in BGP EVPN Type 2 routes?
Flavors can be used to enhance SRv6 instructions to meet more diversified service requirements. Which of the following are flavors? (Select all that apply)
Which of the following types of LSAs does OSPF use to support SR-MPLS?
An LSR (Label Switching Router) supports various label retention modes. Which of the following statements regarding the liberal mode are correct?
Which of the following statements about BGP EVPN principles are correct in a scenario where a VXLAN tunnel is dynamically established through BGP EVPN?
MACsec can provide secure services during MAC-layer data transmitting and receiving. Which of the following services is not provided by MACsec?
Exhibit:
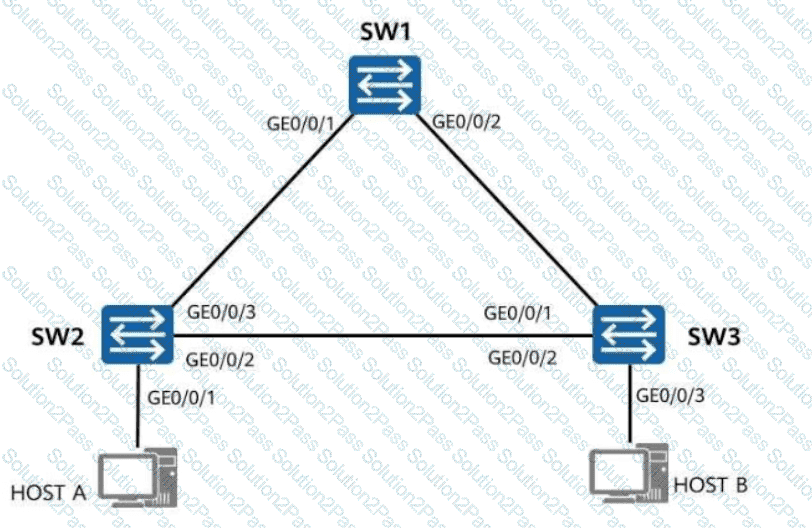
A loop occurs because Spanning Tree Protocol (STP) is not enabled on the network. Which of the following symptoms may occur?
Which of the following statements is incorrect about a BGP/MPLS IP VPN?
In an MPLS VPN network, two-layer MPLS labels are added into data packets before they are transmitted over the public network. Which of the following statements regarding data packet processing are correct?
On a CloudCampus virtualized campus network, service data enters different VNs from physical networks through edge nodes, and the VN that the data will enter is determined by the VLANs to which users belong. Which of the following statements about dynamic VLAN authorization is incorrect?
Among NETCONF operations, the < config > operation may contain an operation attribute, which is used to specify an operation type for configuration data. Which of the following operation attributes is incorrect?
By default, the domain ID of an OSPF process is the same as the process ID. You can run the domain-id command in the OSPF process view to change a domain ID.
Which of the following statements about DHCP snooping is incorrect?
Which of the following inter-AS MPLS L3VPN solutions need VPN user data packets to carry MPLS labels when being forwarded between ASs?
MPLS supports forwarding equivalence class (FEC). Which of the following cannot be used as an FEC allocation standard?
