NSE4_FGT_AD-7.6 Fortinet NSE 4 - FortiOS 7.6 Administrator Free Practice Exam Questions (2026 Updated)
Prepare effectively for your Fortinet NSE4_FGT_AD-7.6 Fortinet NSE 4 - FortiOS 7.6 Administrator certification with our extensive collection of free, high-quality practice questions. Each question is designed to mirror the actual exam format and objectives, complete with comprehensive answers and detailed explanations. Our materials are regularly updated for 2026, ensuring you have the most current resources to build confidence and succeed on your first attempt.
What are two features of FortiGate FSSO agentless polling mode? (Choose two.)
Refer to the exhibit.
A partial cloud topology is shown.
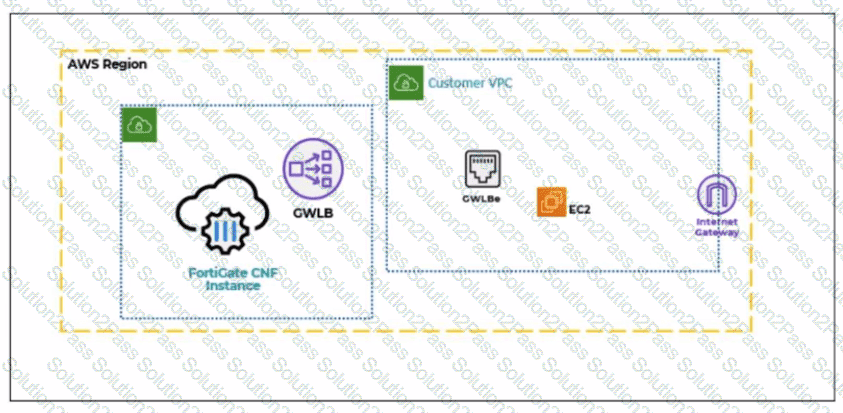
You deployed a FortiGate Cloud-Native Firewall (CNF) in AWS.
During the deployment, which components must the FortiGate CNF create to handle traffic from the EC2 instance?
Refer to the exhibit.

The exhibit shows the FortiGuard Category Based Filter section of a corporate web filter profile. An administrator must block access to download.com, which belongs to the Freeware and Software Downloads category. The administrator must also allow other websites in the same category. What are two solutions for satisfying the requirement? (Choose two answers)
When configuring firewall policies which of the following is true regarding the policy ID? (Choose two.)
Refer to the exhibit.
A routing table is shown
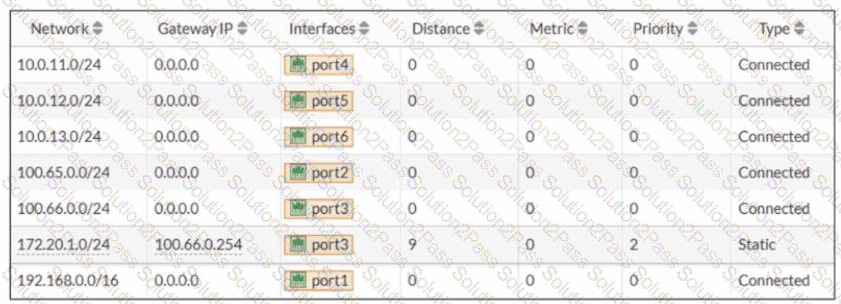
An administrator wants to create a new static route so the traffic to the subnet 172.20.1.0/24 is routed through port2 only. What are the two criteria that the administrator can use to achieve this objective? (Choose two.)
Refer to the exhibit to view the firewall policy.
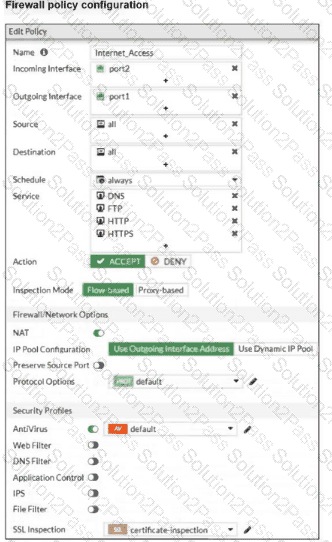
Why would the firewall policy not block a well-known virus, for example EICAR? (Choose one answer)
Refer to the exhibit.
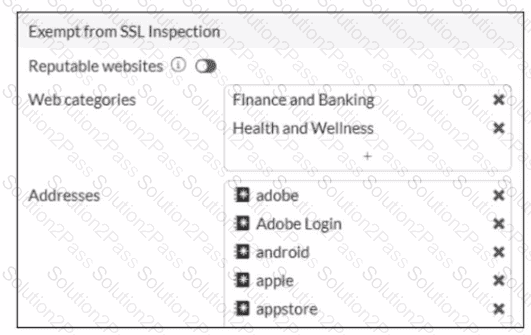
The predefined deep-inspection and custom-deep-inspection profiles exclude some web categories from SSL inspection, as shown in the exhibit For which two reasons are these web categories exempted? (Choose two.)
